Identity and Access Management Devroom
This room is cursed.
– The video volunteer when entering the room in the morning.
Day two stared of great with a some great presentations in the IAM devroom. I woke up early so I could get a seat on the front row and was happy that I did.
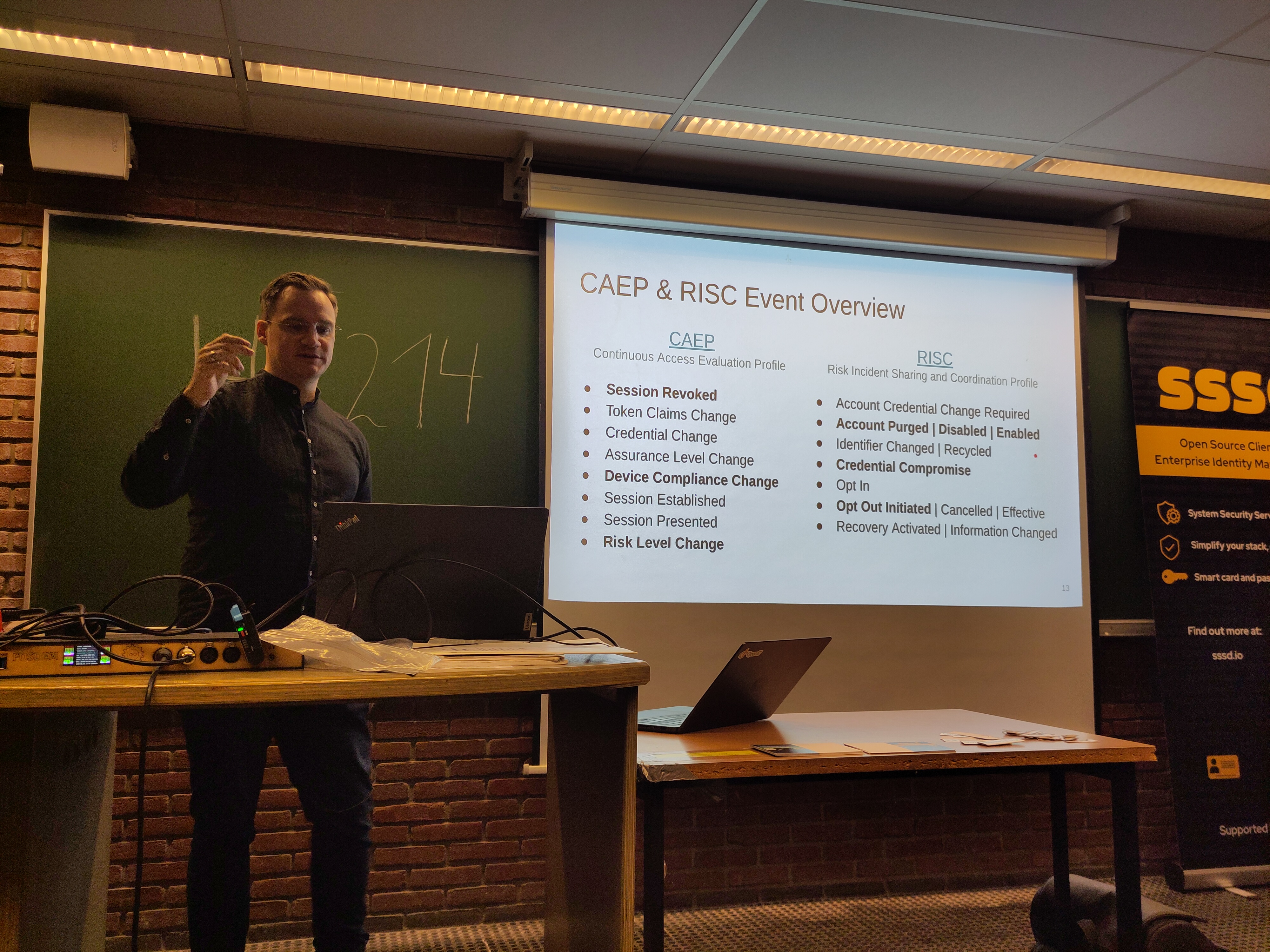 Thomas Darimont giving a presentation on OpenID’s shared signals framework.
Thomas Darimont giving a presentation on OpenID’s shared signals framework.
An Introduction to the OpenID Shared Signals Framework
SSF tries to normalize the signals to do Continuous Access Evaluation
Use Cases:
- Real-time Session Revocation
- Compromsed Account Alert
- Automated User Deprovisioning
Building blocks: Security Event, Transmitter (System emitting event), Receiver, Stream and subscription on events. Security Event tokens are an IETF RFC
Profiles: Set of use cases and events
- CAEP
- Based on sessions
- Evalutaion of access decisions
- RISC
- disaster mitigation
- security risks and inicdnets
Delivery methods are push (RFC 8935) or poll (RFC 8936).
There is also an IETF draft for SCIM Events.
Implementation in Keycloak with pull request 43950 Custom login when receiving events. Next step will be transmitter support.
Questions & thoughts 🤔
- Does the CAPE profile make OpenID connect session managment obsolete?
- Answer: No, different use cases
- For SaaS, how is privacy of the user handled?
- In Keycloak is the logic on how to handle events configurable, if so how?
Nextcloud as Identity Provider? SCIM Client Integration for Multi-Platform Collaboration
Nextcloud X OpenProject
Use scim for automated identity information exchange.
AGPLv3: The only sensible license option for NC apps according to the speaker .
Questions & thoughts 🤔
- Why not use a dedicated IDP?
Now I am a bit confused on what exactly the difference is between the SCIM client and server. I should do a deep div on SCIM.
Keeping applications secure by evolving OAuth 2.0 and OpenID Connect
FAPI 2.0 was published in 2025 targeting more than just banking (e-health, government).
Security assumptions of FAPI 2.0 were well documented.
https://openid.net/specs/fapi-attacker-model-2_0-final.html
Secure your transport layer!
- TLS 1.2+
- Check certificates
- DNSSEC
- Secure ciphers
- HTSTS
OAuth best pratices
- TLS on all endpoints
- No ROPC
- No wildcards in redirct URIs
- Private key JWT client authentication (no public clients)
- Pushed Auth. request (PAR)
- PKCE with S256
- Sender contrained tokesn (mTLS or DPoP)
An API can respond to a API request with a DPoP nonce request. Adding an extra step to an API request, but improving security.
🤔 I wonder if this is always required for DPoP or if the nonce is optional. The RFC says “An authorization server MAY supply a nonce value to be included by the client in DPoP proofs sent.” So I guess it’s optional. See RFC 9449 for details.
Keycloak has builtin client profiles. Which enforces security requirements on clients. Enforced at config and runtime. Rules can be added to a custom profile.
Funny way to convince development teams to keep clients secure: brownouts to speed up the process. Security with a whip!
There is a keycloak conference taking place in Amsterdam in March 2026.
Questions & thoughts 🤔
Error messages in the Keycloak admin UI suck. This could be something that can be improved by the community. If I felt more comfortable with the codebase I could pick it up.
I wonder if the security profiles could be externalised, I have built scripts in the past to validate OAuth client configs against a set of security rules.
Inside ProConnect: Building a Modern Federated Identity Provider for Government Services
ProConnect enables single login for grench government services (public servants, external users)
La Suite numerique a set of open source tools provided by the French Govt.
Demo with one of the best: Visio for vidio confernces.
- User gives email and ProConnect redirect to the correct underlying IDP.
- The designs of the webui’s are alligned.
From FranceConnect to ProConnect
Proconnect has ~40 Idp’s!
SP & Idp Mocks.
http://www.dev-agentconnect.fr/
Identity borkering: Email domain name based routing.
Passkey auht with AMR POP
Identity format for public servants in a professional context.
Testing is free via Espace Parenaires.
Easy install of ProConnect with Docker.
Open Repository on github
Questions & thoughts 🤔
- If ProConnect is a fork of FranceConnect, is the infra / user database / … also forked?
- IF ProConnect acts as an Identity Broker, how does it decide on the Idp to user?
- Is the user identified first?
- Yes, map of email domains to Idp.
- Is the user identified first?
Privacy and Sovereignty in a Post Quantum Open World
Kings & Serfs, Masers & Slaves. Closed source users are software slaves!
Business people hat the word freedom (Choice, competition)
Sovereignty, not just for data but: Software, Networking, Technology.
Users need to control
One more consideration: Quantum Computing
- (re)encrypt data
- VPN’s -> QPN’s
- Need to move towards MFA
We need a community of trusted people.
- Freedom Software
- RISC-V Architecture
- Now moved to swiss
We need sovereign cloud that are security first.
Corporta: Secure sentinel
Community cloud: freedombox.org
Tiny server on SBC.
Also supports fediverse.party software for social networks.
MFA: Hardwayre keys: need to use 2. Has to be open design:
- inspectable
- long life
Working with solokeys an open-source FIDO2 security key.
SUSEID - Sovereign IAM at SUSE
How suse has tackled IAM landscape.
Lot’s of mergers: Multiple password providers, add-ons and bridges.
The ride for an average SUSE Employee
- Open Jira: user +pass
- Open conflunece: user +pass
- Open build service: user +pass
- Bugziall: user +pass
- suse costuomer center: different prompt!
Art21 of nis2 Dora art 5,9,10
-> No SaaS for Auth.
Self hosting comes with costs, (ops, dc, …)
Patroni for HA PostgreSQL Garage for obj storage
Authentik IDP
Existing projects: smallstep KanIDM
New projects:
- stepdance: certifiactes
- ldap SEBIN search + bind
- IDM Merge: Idm Aggregator & Dedup
Credentials for Linux: Bringing Passkeys to the Linux desktop
Passkeys are quite complex.
Passkey = FIDO2 discoverable credential
- usernamesless & passwordless
New FIDO2
- Hybrid flow: Passkey on pohne (qr code)
- synced Passkeys
Modern Passkeys
Phones and password managers Default:
- Google Password manager
- iCloud keychain Third party:
- bitwaden
- oss
requires credential provider API
(synced creendials)
Security keys still for entrprise
Linux desktop needs platform api’s.
Inconsistent api: currently apps (browsers) implement UX themselves.
Containerized (flatpak) apps’ don’t have access to hardware api’s (workaround
--device=all, enables origin bypass)
Solution: a new Credentials api.
- D-Bus
- support for privileged and unprvilegd clients
New componenents:
- lebwebauthn: CTAP/WebAuthn
- credentialsd
Use of xdg-desktop portals for sandboxed apps.
In libauthn: TPM 2.0 (platform) is planned
Open Cahllenges:
- Origin scoping: credentials for your origin should only be accessed by that origin.
- How do we determine origin
- App identity verification?
Prividleged: any origin (browsers) unprvilegd: restricted to specific origin
Cockpit and passwordless login
Cockpit authentication:
- Preferably PAM modules
- SSO, Kerberos, …
- Flatpak app
SSH keys are an example of passwordless but not usable in te browser.
Based on WebAuthn,FIDO2,Passkeys
- ensure origin authenticity
- web domain / hostname / realm differences.
/.well-known-webauthn- Can support multiple origins.
Registering with the “Chromium virtual authenticator enviroment” for testing / demo.
Passkey
- Discoverable
- limited slots
- no username needed, user
- Non-discoverable
- doesn’t store on hardware
Questions & thoughts 🤔
I should look further into discoverable vs Non-discoverable credentials on passkeys.
Fancy slides! I wonder what was used to create them.
Passwordless authentication mechanisms from the GUI (GDM)
GDM: Login on gnome (Password, Smartcard, Fingerprint)
Gnome shell renders the UI. Runs as GDM user To authenticate GDM calls PAM over private dbus servers.
Improved UX: select auth. method.
New web login with OAuth device code flow.
Fingerprint only on lock screen.
Available in SSSD 2.12.0
Two merge requests for GNOME 50
Future enhancements:
- embedded webview
- PAM conversation through fd
- Move GDM into systemd?
Questions & thoughts 🤔
Someone asked a question on using SPIFFE which is used for workload authentication, I guess they were wondering if it’s possible to let an AI agent authenticate to a Linux machine with a gnome desktop this way?
Reduce attack surface or keep compatibility: lessons of sudo-rs and run0 transition plans
US Govt. mandating secure software
- Zero trust
- Secure software development
- Switch to modern languages
Will take long time to transition (ZTA, Post-Quantum).
How to reduce attack surface?
- run0 aims for a system without SUID
- polkit for AuthZ
Reducing attack surface
Sudo-rs: Switching to Rust
- Memory safety
- Thread safety
- Error handling
- Strong typing
Large scale deployments
FreeIPA can centrally manage sudo rules
Generic rules
- sudo added support for regexes
Polkit action defintions are local XML-based files. Polkit authorziation rules are written in javascript, have to be local files.
sudo-rs: missing features
Questions & thoughts 🤔
Is the goal of sudo-rs to have feature parity with sudo?
I should look into how polkit handles fine grained authorziation.
Rust Devroom & Lightning Lightning Talks
Rust Coreutils in Ubuntu: Yes, we rewrote /bin/true in Rust – Here’s what really happened
Pareto rules: 80 of the work takes 20 of the time
What’s next.
Rewrite other GNU utilities.
Questions & thoughts 🤔
GPL debate: Is canonical just supporting this so they can get rid of GPL code in their distro?
CONTRIBUTING.yaml
CONTRIBUTING.md but machine readable
- status
- intentions
- support needs
ECMA standarization track.
https://www.tc54.org/contributing-yaml/
Misconceptiosn heard at FOSDEM about CRA
- No fines for open source projects.
- You can take donations.
- Your employer won’t be liable if you as an employee work on foss
- Releasing FOSS does not mean that you need to fill in compliance documents.
- an open source steward can be useful, but is not required.
- The CRA does not require changes to project processes
- …
Dumb guide to smart TVs
You pay for:
- ads
- Automatic Content Recognition
- Send low quality screenshots to vendor.
- the netflix button
Nu smart TV allows you to turn off all of the anti-features
- dont’t connect it to the internet
- hack your TV!
body.build
Wikipedia bring the best articles, what is the equivalent for fitness?
- Database of exercises
- Applications
- program creator
- calorie calculator
- …
PostgreSQL compatibility index
Not everyone that claims to be PostgreSQL compatible actually is.
Suite to test compatibility.
pacman cache server
I’m not using Arch at the moment so I took no notes 😄.
EU software patents via UPC
ffii.org
GUI vs TUI – Why not both?
Amazing!
web browser -> wayland -> terminal
Render browser directly to terminal
Not interested in smart but funny. https://github.com/dextero/smithay
Git for email
Using a git repo to represent emails as files.
RCL configuration language
Extends JSON by adding variables functions loops …
Can also be used to query
🤔 I wonder what the difference is with Jsonnet.
Gitify your life - 14 years later
Etckeeper, bup, ikiwiki, git-annex, metamonger, vcsh, mr, zsh.
Main track
Open Source Security in spite of AI
Took no notes.
https://daniel.haxx.se/blog/2026/02/03/open-source-security-in-spite-of-ai/
Closing FOSDEM 2026
If we lose our democracies Open Source is irrelevant and goes away!
– RichiH
Talks I would still like to watch later
There were a whole lot of talks that I was not able to watch. Luckily talks at FOSDEM are recorded & avaiable on video.fosdem.org!
Listed talks.